2026年3月11日、医療技術企業ストライカーは、社内のMicrosoft環境の一部に影響を与える障害を検出した後、サイバーセキュリティインシデントを公表しました。同社はSECフォーム8-Kの提出書類の中で、インシデント対応計画を発動し、外部の対応者を動員したと述べています。公表時点で、ストライカーはランサムウェアやマルウェアの証拠はないと報告し、インシデントは収束したようだと述べています。
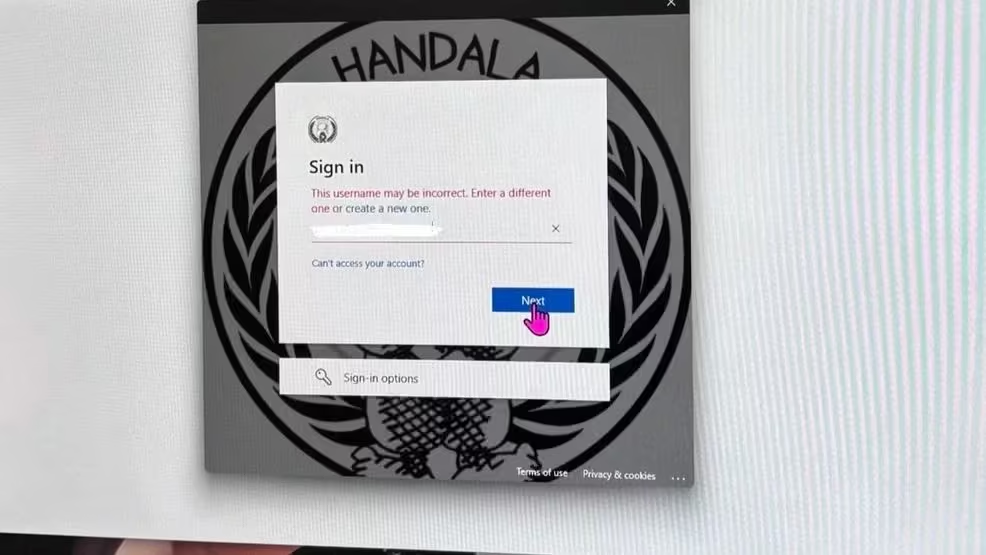
その後、従業員やセキュリティ研究者からの報告によると、社内のデバイスがリモートでデータ消去され、ログイン画面がHandalaのロゴで改ざんされていたことが判明しました。調査によると、攻撃者はMicrosoft Intuneを悪用して管理対象デバイスにリモート消去コマンドを発行し、会社のノートパソコンやモバイルデバイスを工場出荷時の状態にリセットした可能性があるとのことです。Intuneのワークプロファイルに登録されている一部の個人所有のスマートフォンも影響を受けたと報告されています。
攻撃者側は、今回の事件の規模についても主張しています 。独自のチャネルを通じて、20万台以上のデバイスが影響を受け、大量のデータが流出したと述べており、当初は50テラバイト(TB)としていましたが、後に12ペタバイト(PB)にまで数字を引き上げています。これらの数字は未確認であり、攻撃者は破壊工作の際に影響を誇張することが多いため、慎重に扱うべきです。
明らかなのは、これほどの規模の事件は、環境内部での継続的な活動を必要とするということです。最初の侵入経路が不明な場合でも、攻撃者は通常、その過程で身元やネットワークの挙動に関する痕跡を残します。

脅威の主体:Handala/Void Manticore
この事件の責任を主張しているグループはHandalaであり、一部の研究者からはVoid Manticoreとしても追跡されています。Void Manticoreは、破壊工作とプロパガンダメッセージを組み合わせたことで知られる、イランと連携する脅威アクターです。
このグループはこれまで、ITプロバイダー、インフラ事業者、機密性の高いサプライチェーンに関わる企業など、戦略的または象徴的な重要性を持つ組織を標的にしてきました。医療技術企業は、医療提供者、研究環境、製造システムを結びつける役割を担っているため、このエコシステムにおいて特に重要な位置を占めています。
金銭的な動機を持つ多くのグループとは異なり、Handalaの攻撃活動では、しばしば業務妨害および心理的インパクトが重視されます。同グループは、侵害されたシステムのスクリーンショットを頻繁に公開し、盗まれたデータに関する主張を誇張し、Handalaのロゴなどのプロパガンダ画像を用いてシステムを改ざんすることがよくあります。ストライカー事件で報告されたデバイスのデータ消去やログイン画面の改ざんは、このパターンと一致しています。
運用面では、このグループは、自動化されたマルウェア攻撃よりも、手動による侵入を行う傾向があります。攻撃者は侵害されたシステムと直接やり取りを行い、正規のサービスや管理ツールを利用して環境内を移動します。この手法により、攻撃者が環境の把握やアクセス権限の拡大を進める間、その活動は通常の運用に溶け込むことができます。
襲撃の経緯を再構築する
ストライカー事件で実際に使用された侵入経路については、公には確認されていません。以下の再構成は、入手可能な報道と「Handala」の既知の手口を組み合わせたものであり、同グループの過去の活動に基づく合理的な推測も含まれています。
1. 個人情報の不正利用による初期アクセス
MITRE ATT&CK:T1078 – 有効なアカウント | T1110 – ブルートフォース | T1566 – フィッシング
この種の侵入は、フィッシングや認証情報の流用、あるいは第三者のアカウントの侵害によって入手された認証情報の悪用から始まることがよくあります。また、イランの脅威グループは、侵入の足掛かりとしてVPNインフラも標的にしています。
攻撃者が有効な認証情報を手に入れれば、従来のセキュリティ対策の多くを回避して、VPNやMicrosoft 365サービスに認証を行うことが可能になります。
セキュリティチームは、通常とは異なる認証場所や、ユーザーの普段の振る舞いパターンと一致しないログインパターンなど、初期の兆候を頻繁に察知します。
2. 権限昇格
MITRE ATT&CK: T1098 – アカウント操作 | T1484.001 – ドメインポリシーの変更
アクセス権を取得した後、攻撃者は通常、さらなるシステムや機密データにアクセスできるよう、権限の拡大を試みます。
Microsoft環境では、これにはグループのメンバーシップの変更、ロールの割り当て、またはディレクトリのアクセス権の変更などが含まれることがよくあります。これらの操作により、攻撃者は最初に侵害されたアカウントの枠を超えて、より広範な管理者権限を獲得することが可能になります。
これまで正常に動作していたユーザーアカウントによる異常な管理操作は、多くの場合、システムが侵害されたことを示す最初の明確な兆候となります。
3. 偵察と横移動
MITRE ATT&CK: T1018 – リモートシステムの発見 | T1087 – アカウントの発見 | T1021.001 – リモートデスクトッププロトコル | T1090 – プロキシ/トンネリング
権限が拡大すると、攻撃者は環境のマッピングを開始します。
これまでのインシデントで記録されているHandalaの活動には、システム間での手動によるRDP移動や、内部ホストに到達するためのトンネリングツールの使用が含まれます。この段階では、攻撃者は通常、アカウント、システム、およびネットワークリソースを列挙し、重要なデータがどこに保存されているかを特定します。
これらの動作は正当な管理プロトコルを通じて行われるため、振る舞い 異常が指摘されない限り、通常の運用トラフィックに紛れ込んでしまう可能性があります。
4. 認証情報の盗用およびディレクトリ列挙
MITRE ATT&CK:T1003.001 – LSASSメモリ | T1003.002 – レジストリ・ハイブのダンプ | T1087.002 – ドメインアカウントの検出
Handalaの活動に関する脅威レポートによると、認証情報の収集手法が繰り返し使用されていることが示されています。
捜査当局は、このグループが LSASSのメモリ を使用して comsvcs.dll 経由 ランドル32.exe、レジストリ・ハイブのエクスポート、および実行 ADRecon Active Directory 環境を一覧表示するためのスクリプト。
これらの手順により、攻撃者は特権アカウントを特定し、ドメイン全体へのアクセス権を拡大することが可能になります。
5. データの自動収集とスクリプト作成
MITRE ATT&CK: T1059 – コマンドおよびスクリプトインタプリタ | T1059.001 – PowerShell | T1005 – ローカルシステムからのデータ
大規模なデータ収集が手作業で行われることはほとんどありません。攻撃者は通常、スクリプトツールを利用してファイルを検索し、機密データを収集し、転送の準備を整えます。
この目的には、PowerShell やコマンドラインによる自動化が一般的に利用されます。これまでスクリプトが使用されていなかったシステムでスクリプトの実行が確認された場合、それは多くの場合、データ収集やデータ準備作業が行われていることを示しています。
6. データのステージングと流出
MITRE ATT&CK:T1041 – C2チャネルを介した情報流出 | T1567 – クラウドストレージへの情報流出
攻撃者らは、その環境から大量のデータが盗まれたと主張しています。たとえその数値が誇張されていたとしても、大規模なデータ転送には、データの準備、圧縮、そして継続的な外部へのトラフィックが必要となります。
このような活動は通常、データ転送パターンに目に見える異常を引き起こします。特に、通常はその程度の送信トラフィックを生成しないシステムから大量のデータが送信される場合、その傾向が顕著です。
7. デバイス管理を通じた破壊的な行為
MITRE ATT&CK:T1485 – データ破壊 | T1562 – 防御機能の無力化
ストライカー事件において、最も大きな混乱を招いた要因の一つは、エンドポイントを初期化するためにデバイス管理インフラが使用されたことだったようです。
報告によると、攻撃者はMicrosoft Intuneのリモートワイプ機能を悪用し、管理対象デバイス全体で工場出荷時設定へのリセットを引き起こしたとのことです。この手法により、十分な管理者権限を持つ攻撃者は、従来のマルウェアを展開することなく、広範囲にわたる業務の混乱を引き起こすことが可能となります。
また、影響を受けたエンドポイント上のフォレンジック証拠を消去してしまうため、インシデント対応を困難にします。
なぜこの事件が重要なのか
ストライカー社の事件は、現代の侵入攻撃においてますます一般的になりつつあるパターンを浮き彫りにしています。攻撃者は必ずしも高度なエクスプロイトに依存しているわけではありません。その代わりに、彼らはIDとアクセス、および管理制御層に焦点を当てています。
攻撃者がID管理システムへのアクセス権を獲得すると、次のようなことが可能になります。
- 権限を拡大する
- 機密データにアクセスする
- 管理上の手続きを経て進める
- 管理インフラを通じて業務を妨害する
クラウドIDおよび一元管理プラットフォームを基盤とする環境において、これらのシステムを管理することは、事実上、企業全体の管理につながることになります。
セキュリティチームが注意すべき点
このようなインシデントは、破壊的な活動から始まることはめったにありません。攻撃者は通常、混乱を引き起こす前に、その環境内に潜伏してアクセス権限を拡大し、情報を収集することに時間を費やします。
同様の事案を調査するセキュリティチームは、以下の点に細心の注意を払う必要があります。
- 通常とは異なる地理的場所からの認証
- ID管理システムにおける権限の変更
- PowerShell またはスクリプトの異常な動作
- 異常なデータ転送量
- デバイス管理プラットフォーム 内の異常な動作
インシデントに至るまでの行動は、事態が業務の混乱へと発展する前に、侵入を検知し、封じ込めるための最良の機会となることがよくあります。
これらの挙動が実際の環境でどのように現れるか、またセキュリティチームがそれらを迅速に調査する方法については、 Vectra AI Platformの Vectra AI のセルフガイド型デモをご確認ください。


