Security teams do not need more alerts. They need high-quality alert prioritization that answers a simple question: what needs attention first?
That sounds straightforward, but many threat scoring models still start at the event level. They look at a single anomaly, a single rule hit, or a single detection, then assign a fixed urgency. That approach creates noise and blind spots. Modern attacks do not unfold as isolated moments. Even as attacks move faster with AI augmentation, they still unfold as a series of connected behaviors across identities, networks, cloud services, and SaaS applications.
Scoring each event with a uniform risk misses two things defenders need most. First, it misses progression. The meaning of a behavior changes based on what happened before it and what happens next. Second, it misses context. The same behavior can carry very different risks depending on the environment, the asset involved, and the importance of the entity under attack.
Some tools try to improve this with a simple score escalation based on repetition or volume. If the same signal appears three times, the score increases. That can help in narrow cases, but it still distorts reality. Repetition can amplify noisy activity, while a single high-value behavior can be the clearest sign that a real threat is underway.
Vectra AI scoring is built for real attacks. The Vectra AI Platform collects, analyzes, correlates, and prioritizes attacker behaviors across network, identity, cloud, and SaaS. That gives defenders a clear answer to what deserves attention first.
Just as important, the Vectra AI attack signal is high quality. Vectra AI surfaces real attacker behaviors, reduces noise, and helps defenders find threats that other tools miss, including threats that EDR-only approaches may not connect or prioritize correctly. Because Vectra AI sees attacker progression across domains, it can identify attacks quickly and with the context defenders need to act.
This matters because attackers progress through environments over time. They probe, escalate, move laterally, establish persistence, and work toward impact. Defenders need prioritization that understands the story those behaviors tell together. Vectra AI is designed around that reality, combining Vectra AI’s detections, triage, and prioritization engines to surface urgent threats while reducing benign activity that would otherwise consume analyst time.
調査におけるアナリストの思考プロセス
When analysts receive an alert, they usually start with questions like these:
- Is this real attacker activity or expected behavior in this environment?
- How far has the attacker progressed?
- How quickly is this situation evolving?
- Is this tied to an important account, host, or service?
- Why did this entity rise to the top of the queue?
Vectra AI scoring is designed to answer those questions with context, not guesswork. It gives defenders a clear explanation of urgency by combining behavioral evidence, attack progression, and environmental importance into a single prioritized view.
How Vectra AI Scoring Prioritizes What Matters First

1. It starts with a high-quality Vectra AI attack signal
Analyst question: Can I trust this signal?
High-quality prioritization starts with high-quality detection. Vectra AI detections are designed to surface meaningful attacker behaviors, not just isolated anomalies or signatures. Signal is generated using the right model approach for the problem. This comes from classical machine learning techniques, patented algorithms, and state-of-the-art, in-house trained generative AI-based approaches. These focus on behaviors – things that attacks, even when powered by Gen AI tooling, still perform in their attacks.
In addition to the detections themselves, AI is used post-detection to review each detection event and assess whether it presents a risk or is benign given the environment and global factors. This removes benign events, ensuring the events tracked and scored are high-quality and stand as true risks.
2. It understands attacker behavior, not just isolated events
Analyst question: What do these detections mean together?
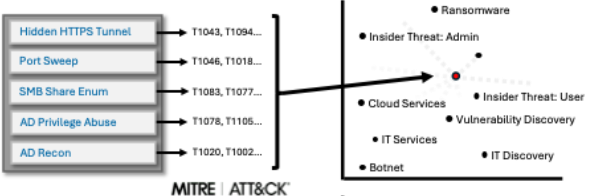
Vectra AI normalizes observed behaviors into a structured understanding of attacker activity, including MITRE ATT&CK-aligned techniques where applicable. From there, Vectra AI correlates techniques into an attack profile that helps defenders understand what kind of activity they are dealing with, whether it looks like an external adversary, ransomware, insider abuse, IT discovery, or another operating pattern. That gives the analyst something much more useful than a pile of independent alerts. It gives them a coherent attack story.
3. It factors in attack progression and velocity
Analyst question: Is this threat accelerating toward impact?
Modern attackers move fast, and AI-assisted attackers will move faster. Vectra AI prioritization considers how behaviors unfold over time, including attack velocity and technique breadth. A single suspicious action may deserve investigation. A rapid sequence of behaviors that suggests credential access, privilege abuse, lateral movement, and command and control deserves immediate attention. Velocity helps separate a possible issue from an active threat that is gaining momentum.
4. It uses rarity and local relevance without overreacting to every anomaly
Analyst question: Is this behavior truly meaningful in this environment?
One of the hardest problems in security is that unusual activity is common, while malicious activity often blends in. Vectra AI approaches this carefully. Vectra AI’s scoring doesn’t treat every rare event as urgent; it uses rarity as one factor to help determine true priority. Meaningful events, like a new host, a rare but risky behavior, or a new device role, are factors that elevate urgency when it matters without turning every difference into noise. The result is stronger signal fidelity and less time wasted chasing activity that is simply unfamiliar.
5. It weighs severity and context together
Analyst question: How dangerous is this behavior if left unchecked?
Some attacker behaviors inherently carry greater risk, especially when combined with the surrounding context. Vectra AI scoring reflects this risk by looking at behavior and context together. Severe behaviors, broader technique coverage, and evidence of attack progression increase urgency. This allows prioritization to reflect the likely operational impact of the threat, instead of relying on a static severity label detached from the environment.
6. It elevates what matters most through importance, privilege, asset role, and customer input
Analyst question: Which entity deserves the fastest response?
Vectra AI urgency scoring is not based only on attacker behavior. It also considers the importance of the entity under attack. AI is used to identify the underlying privilege and asset role. This, combined with customer-defined importance parameters, shapes how an entity is prioritized. That means suspicious activity on a domain controller, privileged identity, sensitive subnet, or business-critical system escalates faster than the same behavior on a less important asset. This is how prioritization becomes operationally useful. It aligns urgency to business risk, not just technical detection.
7. It makes the reasoning visible to defenders
Analyst question: Why did this score rise to the top?
Good scoring should be explainable. Vectra AI presents urgency through a unified score and visible scoring factors so analysts can understand why an entity was prioritized. Instead of forcing teams to reverse-engineer the logic behind an alert, Vectra AI provides them with context up front, including the attack story, the relevant behaviors, and the factors that influenced urgency. This clarity speeds triage, improves trust in the signal, and helps teams act with confidence.
From prioritization to action
Vectra AI scoring answers a simple question: which entities matter most right now?
That prioritization happens at the entity level because attacks unfold over time. The risk comes from how behaviors connect, not from any single detection.
But action still happens at the event level.
Each detection carries the context of the entity behind it, including whether that entity has reached priority. When it has, unresolved priority ensures that all related events stay elevated until the threat is fully addressed, not just partially triaged.
This keeps the model consistent from end to end. Entity scoring focuses attention. Event-level signals preserve that focus through investigation and response.
The outcome of this approach is more than a better score. It is a better operating model for the SOC.
Vectra AI helps defenders move from alert chasing to threat prioritization, reducing the burden of manual triage, connecting behaviors across domains, and surfacing the entities most likely to represent active attacker progression. That means less time spent investigating fragmented signals and more time stopping attacks before they reach impact.
The impact shows up in a few important ways:
- Defenders can focus
In one POV (proof of value) exercise involving nearly 150,000 devices and identities under monitoring, the combination of Vectra AI’s detections, triage, and prioritization reduced the noise to approximately 24 alerts, while still providing coverage for the threats that mattered. That is what high-quality signal and effective prioritization should deliver -- less noise, clearer focus, and better use of analyst time.
- Vectra AI finds threats other tools miss
Because Vectra AI correlates attacker behaviors across network, identity, cloud, and SaaS, it can surface threats that point tools often miss and that EDR-only approaches may not connect into a meaningful attack story. Vectra AI gives defenders visibility into attacker progression, not just isolated events.
- Vectra AI finds threats quickly
Because Vectra AI evaluates progression, velocity, severity, and entity importance together, it helps defenders recognize urgent threats faster. That speed matters because every minute attackers gain increases the chance of impact.
At Vectra AI, that value can be framed in three ways: reducing exposure, removing latency, and maximizing analyst talent. That is what effective prioritization should do.
See Vectra AI in Action
For security teams, the value of scoring comes down to trust. Can the platform help me see what matters, understand why it matters, and respond before the attack progresses further?
That is the goal of Vectra AI scoring. By correlating attacker behaviors across network, identity, cloud, and SaaS, then combining them with attack profile, velocity, severity, privilege, asset role, and customer context, Vectra AI helps defenders focus on the threats that deserve action first.
Vectra AI delivers a high-quality attack signal, helps security teams find threats other tools miss, including threats missed by EDR-only approaches, and helps defenders find and stop those threats quickly.

.jpg)