AIは、攻撃の構築や実行のあり方を変えつつあります。かつてはオペレーターが数日間かけて手作業で行っていた作業も、現在では計画・実行・適応を行うエージェントによって調整されるようになり、人間が介入するのは、システムに指示が必要な場合に限られるようになりました。
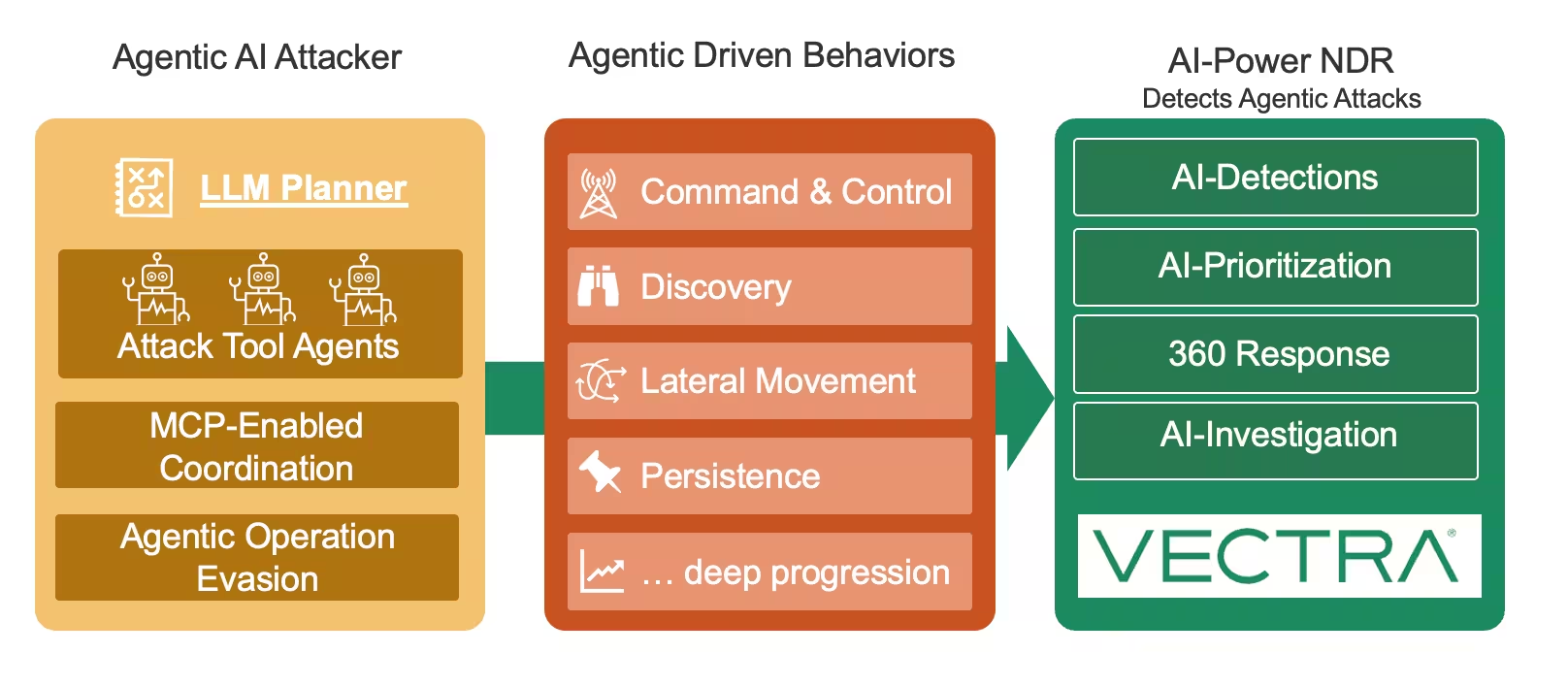
Vectra AIオープンソースの研究では、これが実際にどのような形をとるのかを示しています。それは、MCP(Multi-Agent Coordination Protocol)を活用した自律的なオペレーションであり、標的環境全体で複数の偵察および行動担当の「ワーカー」を調整しつつ、防御側が従来依存してきた多くの痕跡を最小限に抑えるものです。
こうした攻撃は、その本質ではなく、その形を変えるに過ぎない
操作者がAIエージェントである場合でも、攻撃者は依然として目的を達成しなければならない。その目的を達成するには、ネットワーク上から可視化され、最終的には検知可能な行動や動作を実行する必要がある。
実際の侵入攻撃のほとんどにおいて、ネットワークは依然として、標的の発見、移動、連携、およびデータへのアクセスが行われる経路となっています。こうした行動は単なる付随的なものではなく、攻撃そのものです。
我々の研究で実証したこと
本稿 および ここに要約された我々の研究は、MCP対応アーキテクチャが、防御側が従来重視してきた予測可能で反復的なパターンに依存するのではなく、エージェントが必要に応じて接続し、タスクを実行し、結果を報告するという、イベント駆動型の非同期動作へと移行できることを明らかにしている。
重要な点として、この手法では、その活動を一見すると通常の企業向けAIの利用に見せかけることができるため、無害なツールが同様のAI APIパターンを生成している場合、その区別が難しくなる。
また、群知能アプローチが、並行して動作し、情報を迅速に共有し、たとえ1つのエージェントが検知されても任務を継続することで、攻撃能力をどのように向上させるかについても示します。
業界の証拠は一致しつつある
これはVectra AI というだけではありません。
- MCPベースの エージェント型レッドチーム活動: 「AIトラフィックに潜む」では、検出可能な痕跡を低減しつつ、非同期かつ並列な運用とリアルタイムの情報共有を実現するために設計された、MCP対応のアーキテクチャについて解説しています。
- 実環境におけるエージェント:スタンフォード大学が主導した研究では、大学の稼働中のネットワーク(約8,000ホスト)において、AIエージェントと人間のサイバーセキュリティ専門家を比較評価した結果、ARTEMISが総合2位となり、9件の有効な脆弱性を発見し、10人の人間参加者のうち9人を上回る成績を収めた。
- 実世界の事態の深刻化:Anthropic社は、AIが作業の80~90%を担い、人間の介入はごく一部の意思決定ポイントに限られていたという、同社が「AI主導の大規模サイバー諜報キャンペーン」と表現する活動を阻止したと報告した。
ディフェンダーが見逃してはならない重要なポイント
AIは攻撃の大部分を自動化し、ステルス性を高めることができます。しかし、攻撃を進めるためには、ネットワーク全体を横断して操作を行う必要性がなくなるわけではありません。
だからこそ、ツールがエージェント型へと進化し、その活動が正当なAIの利用と見分けがつきにくくなってもなお、ネットワークの挙動に基づく検知は、その有効性を維持し続けるのです。
「自律型AIが攻撃者の動作を高速化し、手作業にかかる時間を短縮することは実証されていますが、ネットワーク全体を横断して活動する必要性がなくなるわけではありません。標的の特定、横方向の移動、通信といった行動は依然として必要です。AIエージェントが攻撃を主導することはできますが、目標に到達するためには依然として同じ経路を通らなければなりません。 我々の研究は、攻撃がまさにこの方向に向かっていること、そしてAIを活用したNDRがそうした行動を検知し、攻撃者を阻止できることを示しています。」
ソフロブ・カゼロウニアン、Vectra AI Distinguished AI Researcher
AI攻撃を防ぐための最良のツールが、AIを活用したNDRである理由
攻撃がより高速化し、適応力を高めていくのであれば、防御側も同様に進化させなければならない。
実務上の意味は単純明快です。特定のツールチェーンやプロンプト形式、あるいは マルウェア ファミリーを追いかけるだけでは、エージェント型攻撃を防ぐことはできません。攻撃者が行わなければならない行動に一般化できる検知が必要であり、その行動が人間主導かエージェント主導かには関係ありません。
AIを活用したNDRは、攻撃者の連携がよりイベント駆動型でAIを融合させたパターンへと移行しつつある中でも、ネットワーク全体への侵入を進行させるために必要な行動に焦点を当てているため、こうした現実に対応するように設計されています。
Vectra AI 、AIの普及が進む中、ハイブリッドネットワークのVectra AI
攻撃者側と企業側の双方でAIの導入が進む中、Vectra AI 成果は2つあります。
まず、Vectra AI 、攻撃を進行させるためにAIエージェントが引き起こすネットワーク上の挙動をVectra AI 、優先順位を付けることで、防御側が脅威を阻止できるようにします。
第二に、Vectra AI 、企業が自らAIを導入する際にセキュリティチームに可Vectra AI 、企業全体における内部のAIエージェントの活動や、公式・非公式を問わずAIの利用状況を監視できるようにします。
AIは運転する主体や、あらゆるものの動きの速度を変えます。Vectra AIはそれらすべてを把握し、それに伴う脅威を阻止します。
---
参考文献
- Vectra AI ブログ、「新技術は新たなリスクをもたらす:MCPを活用したスウォームC2」(2025年8月27日)。
- Janjusevic ら、「AIトラフィックに潜む:LLMを活用した能動的レッドチームングにおけるMCPの悪用」(arXiv:2511.15998、2025年11月)。
- Anthropic、初めて報告されたAI主導のサイバー諜報活動を阻止(2025年11月)。
- Linら、「実環境における侵入テストにおけるAIエージェントとサイバーセキュリティ専門家の比較」(arXiv:2512.09882、2025年12月10日)。


